Malware analysis Malicious activity
4.8
$ 37.00
In stock
(301)
Product Description
Malware Analysis: Protecting Your Network from Cyber Attacks

Malware analysis: Hands-On Shellbot malware – Sysdig
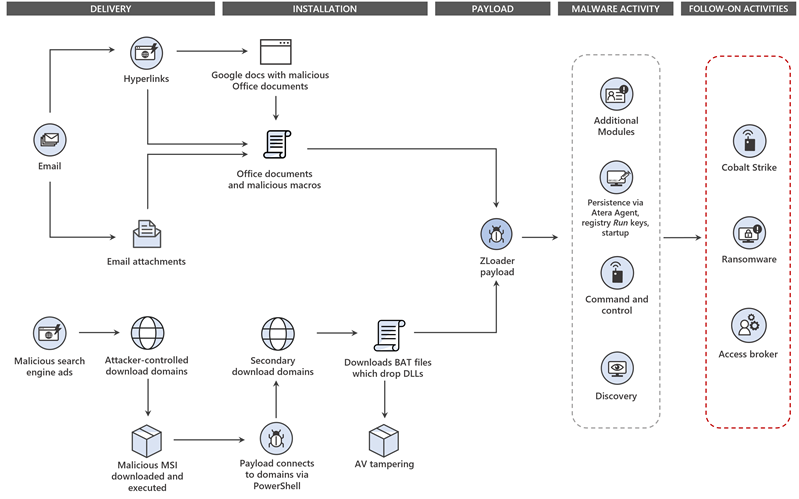
Dismantling ZLoader: How malicious ads led to disabled security tools and ransomware

Malware Analysis: Steps & Examples - CrowdStrike

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights
7 Best Malware Detection & Analysis Tools for Networks in 2023

ChatGPT-powered Malware Analysis

Malware Analysis - Malicious VBA

MalInsight: A systematic profiling based malware detection framework - ScienceDirect
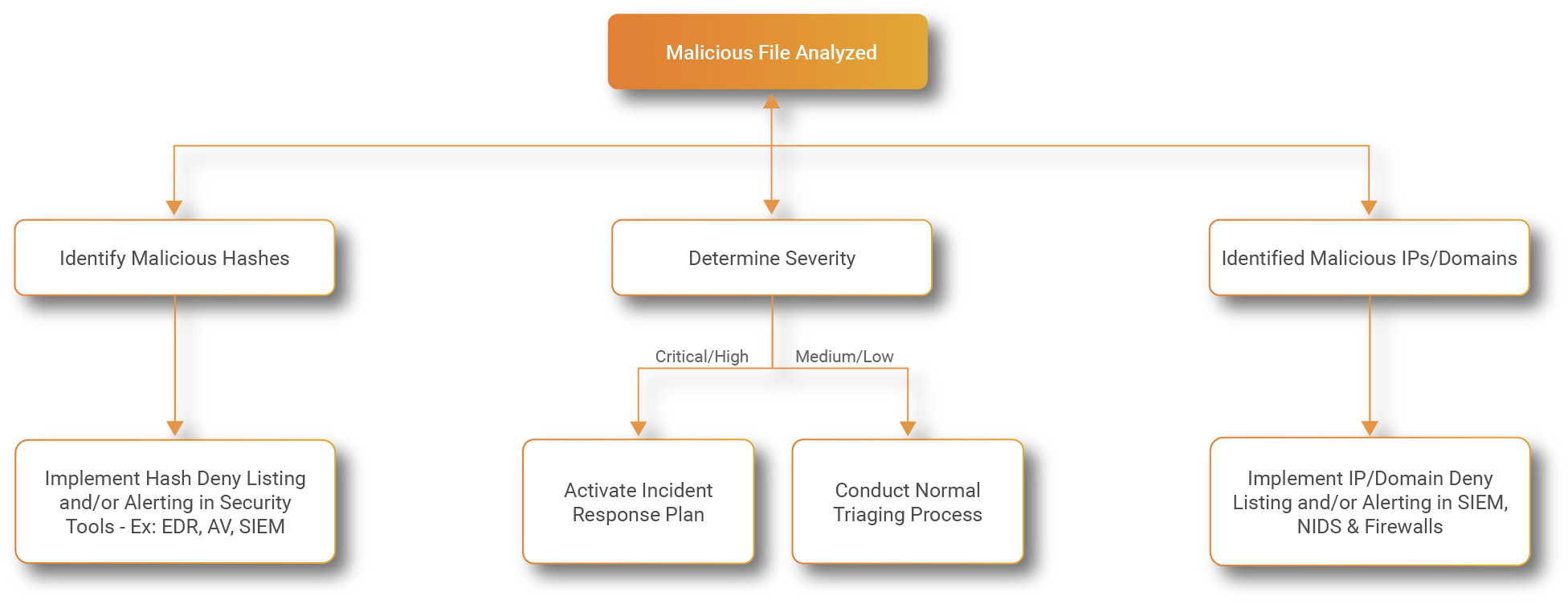
Process flowchart of the malware analysis process during the experiment









